The cybersecurity landscape has shifted dramatically over the past two years, with attackers increasingly leveraging agentic AI to execute breaches at machine speed.
Against this backdrop, Acalvio has emerged as a category-defining vendor that is redefining what it means to deploy a preemptive deception platform.
The recent industry report, How Agentics Redefines Preemptive Deception Platforms, offers an in-depth examination of why traditional defense models are buckling under modern threats.
After exploring the analysis closely, it becomes clear that Acalvio’s ShadowPlex platform represents a meaningful evolution beyond legacy honeypots and reactive endpoint controls.
Table of Contents
ToggleThe Core Problem: A Crumbling Detection Model
Modern security operates under the assumption that breaches are inevitable, yet most enterprises still rely on perimeter tools and signature-based controls.
Sophisticated adversaries now routinely bypass Endpoint Detection and Response and SIEM filters by living off the land with stolen credentials, leaving security teams chasing anomalies long after the damage is done.
Dwell times that stretch into weeks or months remain a stubborn industry problem, particularly when attackers use unmanaged devices or compromised credentials that generate no prior telemetry.
The report makes a compelling case that connecting disparate signals into a clearly malicious behavior pattern is fundamentally difficult, and attackers know exactly how to exploit that ambiguity.
The Shift to Preemptive Defense
Acalvio’s central thesis is that defenders must shift left, moving from reactive detection to preemptive deflection.
By blanketing the environment with deceptive assets that have no legitimate business value, defenders can disrupt the logic loops of automated attackers and force them to waste resources or expose themselves during early reconnaissance.
This is not a theory but a measurable architectural advantage. According to the report, Acalvio outperformed conventional controls during a U.S. Navy cyber defence challenge, with the ability to deflect attacks in head-to-head testing.
The ShadowPlex Architecture
ShadowPlex is built around a patented concept called Deception Farms, which projects thousands of lightweight decoys and honeytokens from a centralized resource footprint rather than dedicating heavy virtual machines to each decoy.
This is the core engineering insight that allows Acalvio to scale across IT, OT, cloud, and identity environments without crushing operational budgets.
The architecture is orchestrated by an AI engine that continuously analyzes the production environment, discovers real assets, and uses generative AI and machine learning to refresh decoys so they mirror the changing terrain.
The result is an automated projection layer that adapts in real time, effectively turning the network into what the report describes as a confusing hall of mirrors for any attacker who lands inside.
Fluid Deception in Practice
One of the most differentiated capabilities in ShadowPlex is what Acalvio calls Fluid Deception, where the level of decoy interactivity adapts based on attacker behavior.
If a low-interaction decoy registers a probe, the system can dynamically escalate to a high-interaction environment, such as a full operating system, to capture richer threat intelligence.
This iterative refinement also allows the AI to adjust deception ploys when operational constraints change, ensuring the deceptions remain efficient and feasible to maintain.
The output is a defense layer that evolves alongside the attacker rather than sitting as a static minefield waiting to be fingerprinted by sophisticated adversaries.
Identity Threat Detection and Response
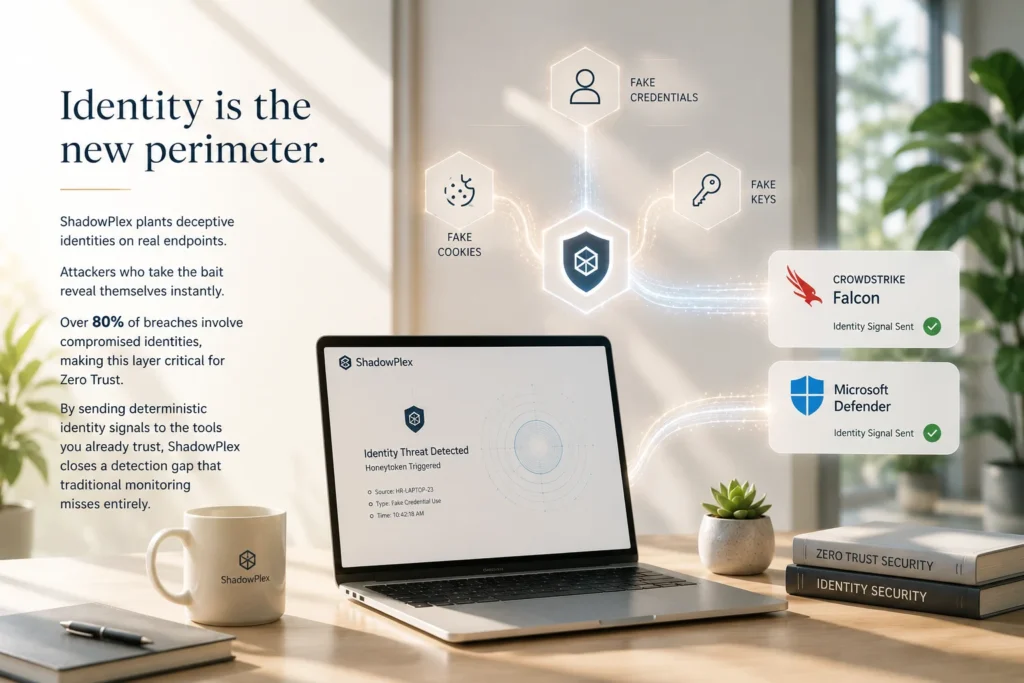
With identity now serving as the primary attack surface, ShadowPlex Identity Protection plants honeytokens such as fake credentials, cookies, and keys directly on real endpoints.
Any attacker who scrapes memory or attempts to use these credentials triggers an immediate alert because no legitimate user would ever interact with them.
Over 80 percent of breaches involve compromised identities, making this layer especially urgent for any organization pursuing a Zero Trust posture.
By feeding deterministic identity signals into existing platforms like CrowdStrike Falcon and Microsoft Defender, ShadowPlex closes a detection gap that traditional identity monitoring routinely misses entirely.
Cloud and Cloud-Native Security
The cloud module extends active defense across AWS, Azure, GCP, and Kubernetes by planting deceptive storage buckets, serverless functions, and IAM roles.
This agentless approach is particularly important for ephemeral workloads where traditional security agents simply cannot keep up with the rate of change in modern cloud environments.
Cloud-conscious adversaries often use built-in primitives to compromise workloads, making detection notoriously difficult for behavioral tools.
ShadowPlex meets this challenge by embedding deception directly into cloud-native attack vectors, catching lateral movement that would otherwise blend into legitimate API traffic.
The Counter-AI Frontier: 360 Deception
The most provocative innovation covered in the report is 360 Deception, A novel capability that inverts traditional deception by making real production assets appear fake or uninteresting to attackers, specifically designed to disrupt the reconnaissance logic of AI agents .
This removes the stable ground truth that automated attackers and AI agents rely on to make autonomous decisions during a campaign.
By altering what attackers can perceive and trust, the platform shifts detection from post-compromise analysis to pre-impact exposure.
The approach is specifically engineered to disrupt the reconnaissance logic of agentic AI, which depends heavily on accurate environmental data to operate effectively at machine speed.
The CHeaT Framework Against Autonomous Agents
Closely tied to 360 Deception is the Cloak, Honey, Trap framework, which weaponizes the cognitive vulnerabilities of large language model agents.
Cloak hides real assets through tokenization quirks and embedded misdirection, Honey scatters synthetic API keys and bogus configuration files that LLMs cannot resist parsing, and Trap uses adversarial prompt injections to push agents into infinite loops or paralysis.
This is among the first frameworks we have seen articulated specifically for defending against malicious autonomous agents rather than human operators.
It represents a meaningful step toward a defense posture that genuinely acknowledges that attackers are no longer purely human in 2026.
Generative AI Working for the Defender
The report dedicates substantial space to how generative AI advances cyber deception, particularly through a six-component framework called Structured Prompting for Adaptive Deception Engineering [ SPADE].
This systematically automates the generation of honeyfiles, API hooks, and honeytokens by combining identity, goal, threat context, strategy outline, output guidance, and output format into actionable prompts.
The practical impact is that security teams can now generate hundreds or thousands of unique, context-aware deceptive artifacts without the labor-intensive manual effort previously required by Deception 1.0 tools.
An LLM-powered Copilot inside ShadowPlex even produces decoy naming conventions tailored to specific industries, ensuring the deceptions blend seamlessly with the surrounding environment.
Competitive Differentiation in a Crowded Field
Acalvio competes against XDR consolidators such as SentinelOne with Attivo, Proofpoint with Illusive, and Zscaler with Smokescreen, alongside specialists like CounterCraft and Thinkst Canary.
Its competitive moat is built on patented Fluid Deception architecture, fiercely vendor-agnostic integration, and AI-driven automation that eliminates the manual tuning burden of older deception products.
Unlike Fortinet or Fidelis, which lock deception into proprietary fabrics, Acalvio integrates natively with the tools security teams already use, including Microsoft Defender and Palo Alto Cortex XDR.
This vendor-agnostic posture creates workflow gravity and embeds the platform deeply into existing SOC operations without forcing rip-and-replace decisions.
User Experience and Operational Fit
The platform is designed to be invisible to defenders rather than imposing yet another console on overworked analysts.
Verified deception alerts flow naturally into Microsoft Sentinel workbooks or CrowdStrike Threat Graphs, meaning analysts experience the value without ever leaving their familiar dashboards.
Pre-packaged, AI-driven playbooks cover common use cases such as ransomware containment and insider threat detection, accelerating time to value significantly.
For midsize enterprises that lack dedicated deception engineers, this approach removes the historical barrier to entry that crippled the first generation of honeypot tools in the 1990s and 2000s.
Sector-Specific Impact
Healthcare environments must protect IoT and IoMT devices that cannot run standard agents, and ShadowPlex projects decoys mimicking these medical systems to catch ransomware before it reaches patient care infrastructure.
Financial services teams seed fake shadow admin accounts and database connections to trap low-and-slow attackers during reconnaissance, well before any fraudulent transfer can be authorized.
The FedRAMP Ready status also positions Acalvio for high-stakes federal deployments, validated by its first-place finish in the U.S. Navy’s Cyber Defense Challenge. These results signal that the platform performs under genuinely adversarial conditions and not just in vendor marketing demonstrations.
The Verdict
The report convincingly argues that Acalvio is reshaping the deception category from a niche curiosity into an enterprise-grade, AI-driven preemptive control layer.
By weaponizing agentic AI for the defender and combining it with patented Fluid Deception, ShadowPlex delivers high-fidelity, deterministic alerts that close detection gaps left open by traditional EDR and SIEM tools.
For CISOs grappling with alert fatigue, extended dwell time, and AI-augmented attackers operating at machine speed, this platform offers measurable ROI through reduced breach impact and faster containment.
The future outlook envisions deception becoming a standard enterprise control layer alongside endpoint telemetry and identity governance, and based on the evidence in this report, that future feels less like an aspiration and more like an inevitability worth budgeting for today.